‘Loose Lips Sink Ships’ was printed on a propaganda poster during World War 2. It was one of the key messages from the ‘United States Office of War Information’, which urged citizens to avoid careless chatter that could potentially undermine war activities. The same risk is relevant for companies today as information in the wrong hands may lead to excessive losses.
In this two-instalment article, you will learn a few things about publicly available information, namely:
- How information can be exploited (it is easier than you think)
- Which kinds of information may be harmful and dangerous to your company (there’s more than you think)
- What can be done to reduce the likelihood of a successful attack by controlling information (you can act today)
Throughout the article, you will learn about tools and terminology that may assist you in collecting key data on your company as well as strategies to reduce potential losses.
This is the first article in a series of two. The next article will be published soon, so keep an eye on our website and LinkedIn page.
Manage the company’s attack surface
An attacker will always seek to increase the likelihood of a successful attack. A crucial factor in this regard is understanding the company’s internal setup and defences, which will determine the target, strategy, and method of attack. This type of information, intelligence, is a collection of data points gathered in the first phase of a (cyber)attack: reconnaissance.
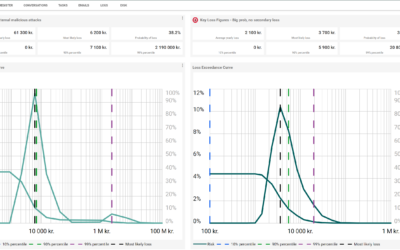
By collecting and mapping publicly available (‘open source’) information about the company’s attack surface, you acquire knowledge which may be utilized in a quantitative risk assessment, ensuring better estimates of the frequency of loss events. This area is often referred to as Open Source Intelligence (OSINT).
Measurements make you capable of reducing the uncertainty of risk. These publicly available data are relevant for your risk assessment, like how the number of machines that have received timely security updates is important in your risk assessment. And you are measuring that, aren’t you?
”If you know neither the enemy nor yourself, you will succumb in every battle.”
Sun Tzu, The Art of War
How may information be exploited?
Criminals are interested in stealing personally identifiable information and trade secrets. These types of information may be used to effectively blackmail companies, customers, and staff by threatening to publish the data.
Companies are known to protect their ‘crown jewels’ well, but seemingly trivial information about software solutions, internal setup and contact information on staff often fly below the radar. This kind of information is, however, used by criminals to increase the odds that their attack is successful.
To identify these trivial but potentially harmful pieces of information, we need to know how they could be exploited.
Trust, fear, and other feelings
Generalisation: ‘Most people wish to fit in. They trust authorities and want others to like them. If someone does something for you, you would like to repay the favor. Generally, we are inclined to help others – if someone asks, you will answer. That is, in essence, how questions function – they demand an answer. Humans strive to follow the rules and follow the pack to avoid negative attention. If someone tells us something we already know, it is easy for us to trust them.’
Most people could partially or entirely fit into the above generalization. When criminals manipulate their targets to commit to a certain action (‘click this link’) or share confidential information (‘send me your bank account information’), they exploit our inclinations as humans, as described above, to engineer a story that allows them to proceed the attack. This strategy is called ‘social engineering’.
It is important to understand that simple information about the day-to-day activities in the company, which in isolation are neither harmful nor secret, may be of great value to an attacker. They use bits and pieces of information to expand on their story to the next person that they are in contact with; department structure, individual staff’s areas of work, internal jargon, vacation plans, approval procedures, screenshots of software from a manual on the company’s website, etc. These are all potentially useful pieces of information. Everything is relevant and can be used – even to the point that a project manager with the right access discloses the source code of the company’s newest phone to a hacker.
The technical information
Companies use their websites for various purposes: to conduct marketing and sell their products, convey contact information for the company, and sometimes to convey the contact information to some or all employees. Perhaps the website is a webshop with integrations to an ERP solution with prices and stock status. Perhaps there is software in place that allows staff to connect to the system using a remote access solution.
These IT solutions are exposed on the internet. The IT solutions are built, structured, and named logically for humans and other systems to work with them effectively, and may hint at how defences are set up. The IT solutions are often very helpful in providing information that increases the system’s usability. The systems could also inadvertently be configured in an insecure manner to increase usability or, quite simply, by oversight.
There are many good and obvious reasons to why you are NOT ALLOWED to access other companies’ and people’s IT infrastructure via the internet. ONLY conduct tests on yourself and your company, and ONLY with written permission from management. It is your responsibility to understand what you can and cannot do.
In Denmark, however, you can browse publicly available databases and services freely.
Examples: www.cvr.dk, www.google.dk and wwww.skraafoto.kortforsyningen.dkExample 1
Using search engines like www.shodan.io, anyone can browse databases of IT infrastructure that are connected to the internet.
A company in Phoenix, USA, has an outdated web server (Microsoft-IIS/6.0), which has not received security updates since 2015. It shows that this server has at least 5 vulnerabilities from 2008 and 2009.
A report from the security firm Palo Alto indicates that criminals scan the web for systems with a particular vulnerability within just 15 minutes of the vulnerability being disclosed.
It is possible to configure servers not to share information about their type and version number, which reduces the probability of having vulnerabilities easily discovered. In the example above, however, the server should have been replaced by 2015 at the very latest. By browsing vulnerability databases such as https://nvd.nist.gov, you can find details about specific vulnerabilities, and in conjunction with other databases, such as www.exploit-db.com, you are able to find methods to exploit these vulnerabilities.
Three recommendations:
- Consider whether it is necessary to expose a system to the internet in the first place. A website – yes, that should be online. The site ‘intranet.company.com’, on the other hand, should likely only be accessible internally or through a VPN.
- Ensure that security updates to hardware and software happen automatically and promptly.
- Always replace hardware and software before end-of-life.
Example 2
Many companies use marketing tools such as Mailchimp to distribute newsletters via e-mail. For these systems to be able to send e-mails on behalf of the company while avoiding being flagged as spam, some technical internet domain configurations are necessary. The fact that the company is using Mailchimp would then be exposed to these configurations. This could be exploited, for instance, by sending a phishing e-mail directly to an employee in marketing.
Three recommendations:
- Ensure that the IT department creates and maintains a register of systems that are exposed to, and used on, the internet. Understand the threat it poses and make it difficult to identify named systems.
- Ensure that all employees are aware of how internal information can be exploited by malicious actors.
- Implement procedures for verification of identity and for handing over any kind of information.
The less obvious, but dangerous, information
Seemingly trivial and harmless internal information may also be exploited. It is virtually impossible to restrict all types of information, yet some guidelines and awareness about the topic can put you on the right track.
Example 1
A company website has a detailed organizational chart published on it. The chart holds the contact information of the company’s employees, including name, title, department, e-mail, and phone number.
Three recommendations:
- Reduce the level of detail on the website. Direct numbers or mobile phone numbers might not be necessary.
- Avoid having information on all employees on the website. Some types, e.g. student helpers, could be more susceptible to phishing or blackmail.
- Ensure that employees are trained not to trust a person because they have knowledge of publicly available information. A person on a phone call who knows the CFO’s private address and that he plays tennis on weekends should not be given further information on that background alone.
Example 2
An employee has posted a picture of an anniversary cake on Instagram. The cake is on a Canon copy machine next to the door to ‘Meeting room A.6’ and has ‘Congratulations to Marianne who has managed to endure us for 10 years!’ written on it.
Three recommendations:
- The employees must understand that pictures with internal information can be exploited if shared on the internet. Ensure that this is a part of the awareness training.
- The information security policy, employee handbook or similar should include guidelines or rules regarding the employees’ use of social media.
- Conduct regular searches on the internet or establish automated surveillance to manage information published both from and about the company.
Example 3
A new employee has posted a picture of his onboarding package from the company on LinkedIn. The picture shows a t-shirt, an iPhone, a ThinkPad laptop, and a keycard on a key hanger with the company logo on it.
Three recommendations:
- Ensure that new employees (as well as those that leave the company) are given specific, written instructions which underline that publishing pictures of keycards and other equipment are not allowed.
- Ensure general awareness training on practice for physical access and the use of social media.
- Conduct regular searches on the internet or establish automated surveillance to manage information published both from and about the company.
In summary
Initiate these three activities to protect your company against the exploitation of information:
- Map your attack surface
There is a range of tools that you can use to map and understand your own attack surface. The cost of these varies from free to expensive. We will cover this aspect in the second instalment of this article. To understand your company’s attack surface, you should always include historical data, which will ultimately reduce uncertainty in a risk assessment.
- Analyze and understand the attack surface in tandem with the risk level
Ensure that you understand what information can be exploited when combined with other pieces of information. This will assist you in deciding on which actions to take to reduce risk.
- Reduce the likelihood that information is exploited
An important part of the awareness effort is ensuring that the rules on sharing information are explicit in the company’s policies, procedures, and employee guidelines. Be mindful of circumstances we cannot change: some information is inherently public, and other information is easy to get your hands on, and criminals will attempt to manipulate us with this. There should also be a focus on technical measures to minimize the attack surface as much as possible.
In the second instalment of this article, we will pinpoint and discuss tools and methods that may be used to gain insight into the company’s attack surface and ultimately reduce the uncertainty in assessing the company’s risk level.
So, stay tuned.
“To know your Enemy, you must become your Enemy.”
Sun Tzu