A skilled offshore engineer with whom I collaborated gave me a very concrete example of the application of risk appetite. The height of a drilling platform is set according to legislation and standards but also according to the company’s risk appetite. How big a wave must the platform be able to withstand? The platform, able to withstand the 100-year wave, is higher and considerably more expensive than the platform that can “only” withstand waves lower than the 50-year wave.
That is understandable. It reminds us that risk appetite is a real management tool for our security work. It forces us to decide on “enough”. Because it varies from company to company, risk appetite must be determined carefully because it can have very large and far-reaching consequences.
The issue of risk appetite is an example of a good opportunity for collaboration between IT and the management/board of directors. If we don’t involve each other properly in this work, risk appetite becomes this arbitrary quantity that makes no difference. In that case, the IT security work is controlled by something else. It could be laissez-faire or fearmongering by people with an interest in selling their products and services.
All activity entails risk, and the question is, therefore, not whether you have risk but how much risk you can accept in your activity. Risk appetite is the level of risk that the company is willing to accept in order to achieve its objectives. The higher the appetite, the higher the willingness to lose in working toward one’s goals.
Risk appetite or risk tolerance?
Let’s reverse the conceptual confusion – is it called appetite or tolerance? In the financial sector, it’s called tolerance. In appendix 5 of the executive order, it’s stated: “… to ensure that risks are identified, analyzed, measured, handled, monitored, reported and are within the company’s IT risk tolerance“. In most other places, it is called appetite. We use the term appetite in this post.
Risk appetite is Very common but not that useful
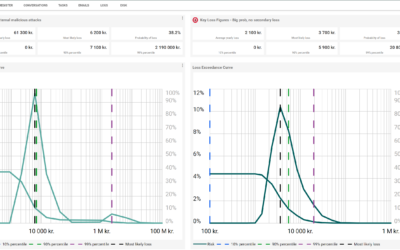
Most use a qualitative ranking of the risk appetite. You typically define a staircase consisting of some statements that describe a certain style in terms of willingness to take risks. In the example below there are 5 steps.
It can be a small starting point for a discussion, but it’s insufficient for an actual, binding determination of the risk appetite. It is impossible to use it operationally. What does it mean, e.g., to move from Minimal to Cautious? Or what difference would it make to IT security work if we moved from Hungry to Open? I’m just asking.
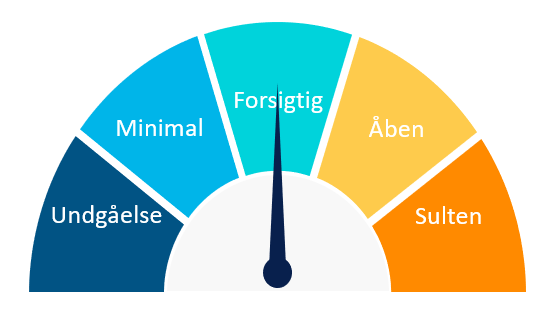
Another qualitative tool that is frequently used is the color codes in a risk matrix.
Here, it’s the boundaries between the colours red, yellow and green that describe the appetite. Red is unacceptable, yellow must be observed, and green is acceptable. We have dealt with the problems with risk matrices in a separate article (see possibly the article Risk matrices for IT risk assessments – the most used method and why it doesn’t work). Using the matrix to determine the appetite contains several problems, which the article addresses.
A well-defined risk appetite, in contrast to the above examples, must be able to provide a clear input to the decision-making process. Below:
- An understanding of the current and future level of risk in relation to the appetite. If our risk level is above the appetite, we must draw up a plan for reducing risk.
- An understanding of where the risk appetite is exceeded. Is it the frequent “cheap” events or is it the extremely rare ones that exceed the appetite?
- An understanding of the cost of mitigating activities (activities aimed at reducing risk) in relation to the actual reduction of the risk level.
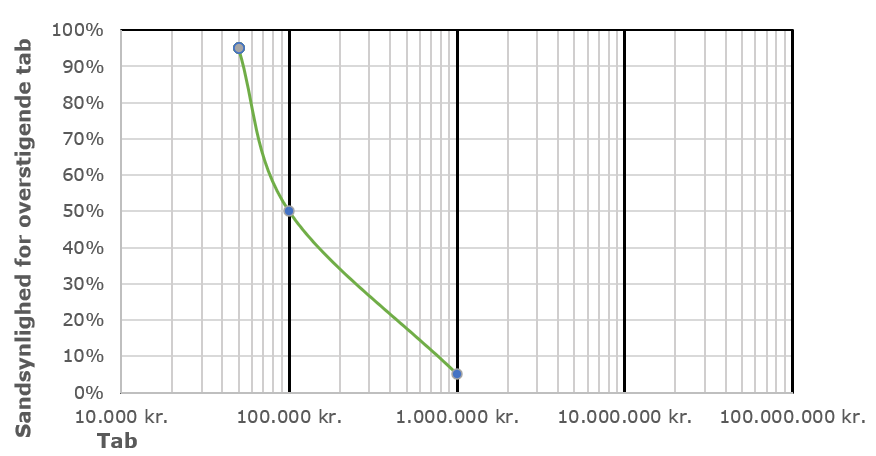
At ACI, we see only one passable path to deliver such risk appetite. We will have to define our risk appetite quantitatively in kroner and euro. What are we willing to lose in kroner with a certain probability? It will deliver on the above checklist and communicate in a way we can all relate to. We will now shift the focus to how. In this article we now look at the simplest way to define our appetite quantitatively.
First, we will define the process. Then, we will test the process in a real-world example.
The process of defining the risk appetite
We will refrain from entering the discussion about who should define appetite. Standards and legislation handle that task very well. We just concentrate on how it can be done.
First, a risk appetite should be defined individually for areas that are very diverse. For example, in the IT area, the appetite is defined individually since the areas of threat (e.g., internal errors and deficiencies and cyber-attacks) are typically very diverse. We typically, and for good reasons, have more of an appetite for losses as a result of internal errors and omissions than losses as a result of cyber-attacks.
For each of the areas, a discussion is held with representatives from the company who can define the risk appetite. That would typically be C-level employees with an overview of the company’s overall finances and potential losses.
The process follows six steps:
- We invite top management to a discussion about risk appetite. You prepare them that it will not be the usual red, yellow, green discussion. No, this time they get to work.
- The meeting begins with a brief calibration of the participants. Participants must be ready to engage in system 2 thinking rather than hip-shooting. Simple calibration exercises can contribute to that. See our article on calibration.
- During the meeting, we ask questions in the form: “What are we willing to lose annually on [INSERT THREAT AREA] with the probability [INSERT PERCENTAGE]. Enter your answer in DKK”.
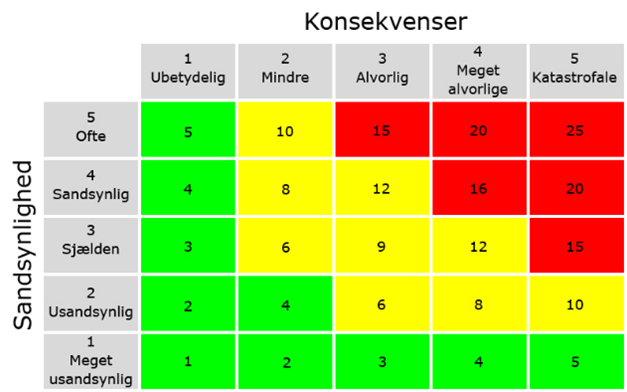
- When we have defined three (or more) data points, we interpolate between the data points and get a “curve for risk appetite”. In the example below, three data points are given for risk appetite. Here you are willing to lose DKK 25,000 annually with a 95% probability (first point on the left), DKK 500,000 annually with a 50% probability (middle point) and DKK 30 million. DKK annually with a 5% probability (extreme point on the right).
- The chart is discussed and adjusted accordingly. Typically, you enter the graph in different places and discuss the consequence of the appetite. If you are e.g., willing to lose 1 million DKK with approx. 30% probability annually.
- The meeting ends with the participants approving the risk appetite.
- The process is repeated for a new threat area.
example of a simple quantitative determination of risk appetite
As a risk analyst, you want to understand what the company is willing to lose with a probability in a given threat area. Let’s take an example in the area of external malicious attacks (cyber). You have invited the CEO and CFO to a meeting about risk appetite in the area of cyber. The meeting begins.
Risk analyst, “Welcome to a discussion about risk appetite in the cyber area. First, I would like to remind you that cyber is a real threat to our business. Cyber incidents are likely for ours just like any other business. Since security costs a lot of resources and can limit our flexibility, it’s important that we establish a level of security that corresponds to our appetite. Do you agree and are you ready?”
CEO and CFO, “We agree and are ready.”
Risk analyst: “Good. I will give you three probabilities and ask you to submit an acceptable loss in DKK. It may seem a bit abstract, but I’m sure you can relate losses with a probability to other areas of our company. You could perhaps think about the placement of liquid assets, where you also decide on the extent to which you are willing to lose with a certain probability. Let’s begin. First question, what amount are we willing to lose with a 95% probability annually in the cyber space (so an almost certain loss)?”
CEO and CFO, “DKK 0.”
Risk analyst, “Yes, that could be nice. However, it is not possible to reduce risk to 0 unless we completely stop using IT. Is that what you want?”
CEO and CFO, “Ha, Ha, OK. Joking aside, what we’re saying is that we are not willing to lose very much on cyber. Shall we say DKK 50,000 annually?”
Risk analyst, “Noted. What amount are we willing to lose by 50% (equivalent to a heads or tails) annually in the cyber area?”
CEO and CFO, “Let’s set it at DKK 100,000.”
Risk analyst, “What amount are we willing to lose at 5% annually in the cyber area?”
CEO and CFO, “Let’s set it at DKK 1,000,000.”
Risk analyst, “Thank you for these three data points. When I plot your data points in a curve with a logarithmic scale, it looks like this. Are you satisfied with that, and do we agree that everything that falls on the left side of the curve is acceptable and what falls on the right side is unacceptable?”
CEO and CFO, “It looks OK for now. But it would be nice to see what our current level is in the same presentation.”
Risk analyst, “We are in the process of calculating the current risk level and will return when the result of the risk assessment is available. I can prepare you for the fact that the cyberspace can contain extreme but rare losses that are greater than 1 million. DKK, but let’s get back to it”.
The meeting ends. I don’t know about you, but isn’t that a better discussion than having to place the boundaries between green, yellow and red in a risk matrix?
Summary
- Risk appetite is the level of risk that one is willing to accept in order to achieve one’s objectives.
- The qualitative assessment of risk appetite is not applicable in practice.
- A simple quantitative determination of the risk appetite can be done through a “what-are-you-willing-to-lose-with-x%-probability” discussion with the executive board.
- The risk appetite can be presented in a risk appetite curve. One curve overall and one curve per area.
Risk appetite is an important part of risk management. Equally important is understanding your current level of risk. We will look at that in other articles.
So, stay tuned.